Hi all,
i have a requirement to deny default confd RPC commit, as the commit should be done only by an app using maapi APIs.
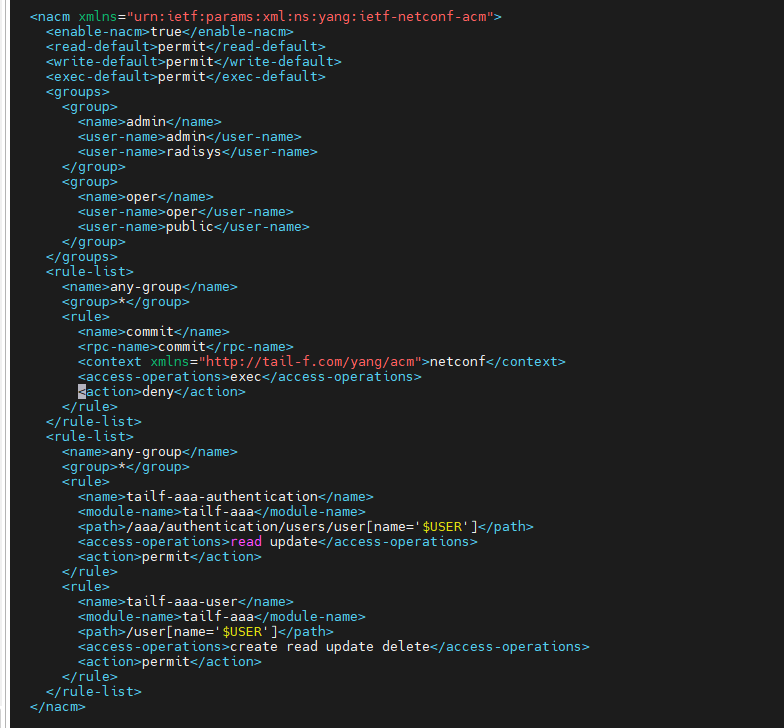
I have added a rule-list to aaa_init.xml as below to deny the commit RPC , but it is not working,
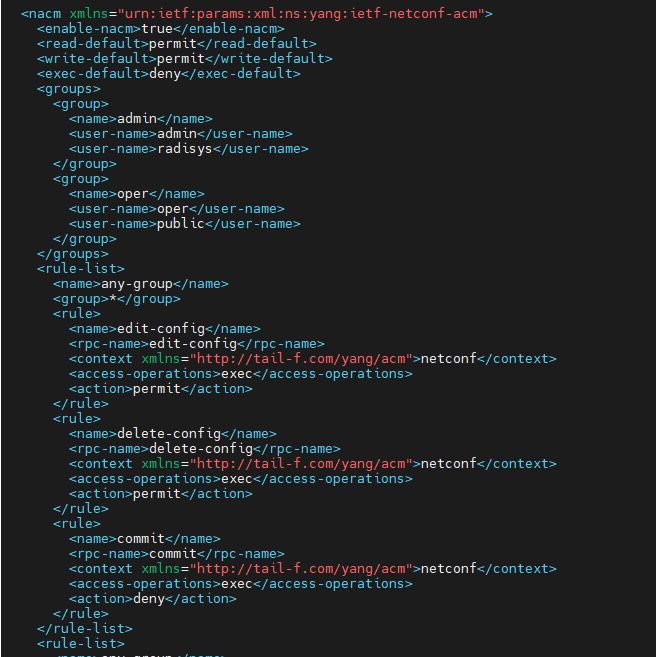
also i have tried below changes as well
true
permit
permit
deny
admin
admin
radisys
oper
oper
public
any-group
*
edit-config
edit-config
netconf
exec
permit
delete-config
delete-config
netconf
exec
permit
commit
commit
netconf
exec
deny
but with this edit-config/get-config/delet-config nothing is working. is the isse is due to i am trying to deny an default RPC?
kindly let know what is missed thing here.
Thanks
kamala
As you suspect, there is an implicit commit that does not trigger NACM rules if you are writing straight to the running DB with NETCONF. If want to continue to write straight to the running DB, you might just deny the edit-config and delete-config RPCs to never let the configuration get in.
If you want to observe the denial of commit messages, you can write changes to the candidate DB and then issue a commit that can be denied. The NACM configuration with the new ‘block-commits’ rule looks like:
rule-list admin {
group [ admin ];
rule block-commits {
rpc-name commit;
action deny;
context netconf;
}
rule any-access {
action permit;
}
}
And then as example, we can write a new user to the user table with an edit-config stored in a file.
edit-config-candidate.xml:
<edit-config>
<target>
<candidate/>
</target>
<config>
<user xmlns="http://tail-f.com/ns/aaa/1.1">
<name>testuser1</name>
<description>test user #1</description>
</user>
</config>
</edit-config>
and then send with
netconf-console --rpc edit-config-candidate.xml
This will put the configuration into the candidate DB. Then send a commit with:
netconf-console --commit
and you will see
$ netconf-console --commit
<?xml version="1.0" encoding="UTF-8"?>
<rpc-reply xmlns="urn:ietf:params:xml:ns:netconf:base:1.0" message-id="1">
<rpc-error>
<error-type>protocol</error-type>
<error-tag>access-denied</error-tag>
<error-severity>error</error-severity>
</rpc-error>
</rpc-reply>